Stonewalling & silence over data breaches
BitDepth #1378
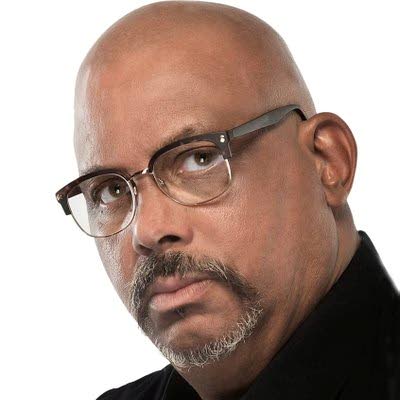
MARK LYNDERSAY
THERE was a moment, while working on this piece, that I hesitated.
I'd invested some effort – but not that much, surprisingly – into exploring the status of the data dump of sensitive corporate information exfiltrated by Hive Ransomware from Massy Distribution.
Now, THE download was running.
A compressed Zip file clocking in at 216GB of company information, legal documents, personnel records and other personally identifiable information (PII) that the ransomware group had first downloaded from Massy and then encrypted on its servers.
A half-day into the download, with 1GB of data pulled down and at least eight more days to go, I terminated the download and the temporary file evaporated.
There was too much about this that seemed untidy, gray and frankly, criminal to continue.
It didn't feel right, but then, neither did Massy's continuously ignoring repeated requests to interview relevant members of their IT team and get the story from their side.
An insistent stonewalling of media investigation into data breaches has become the norm in Trinidad and Tobago.
I know of four major ransomware breaches in this country; only three of which (ANSA and the PoS City Hall are the others) have been reported. In each case, executives declined to discuss the matter in any depth, preferring legally safe PR denials of any customer or business impact.
Last week, Massy issued a press release that described reporting on the incident as "speculative and inaccurate." It was not.
If anything, it was excessively cautious and responsible, as you might expect when discussing the business of a major advertiser.
BITCOIN RANSOM
On April 28, Massy Stores reported disruptions to their capacity to serve customers and eventually explained that the cause was a data breach. The company insisted that customer information was not at risk.
Red Packet Security noted on July 12 that Hive had posted data related to the breach online (https://bit.ly/3VBxIwP).
In the evolving ransomware landscape, hackers prefer a double-barrelled assault. Having gained access to a company's systems, malware will infiltrate as far as it can while surreptitiously downloading what it finds to darkweb servers.
Then the malware encrypts the data accessible to it on the company's servers and a ransom is demanded, normally payable in Bitcoin.
A "proof pack" of the Massy data revealed that the company's business information was in the wind, but it wasn't until September 19 that the full dataset was dumped to the dark web.
According to an expert cybersecurity source, "The files are provided by the hackers in a compressed zip folder with a size of 216.1 GB that contains the company's files. When uncompressed or unzipped that file size is much larger."
The source, who has viewed the data dump, explained that the Zip archive contains, 87,550 folders containing 704,047 files.
"Included are financial records (accounts receivable, accounts payable, budgets, banking, financial statements, internal audits), human resource records (staff photos, surveys, staff listing, job descriptions, events, claims) and operations information."
NO LOCAL LAWS TO COMPEL A COMPANY
On October 08, Massy Distribution Jamaica reported a data breach and the following day, a 17 GB cache of the Jamaican company's data was dumped on the darkweb (https://bit.ly/3szLIK4).
Unlike TT, Jamaica's laws specify exactly what a company must do after discovering a breach.
The TT Cybersecurity Incident Response Team (ttcsirt.gov.tt/) responded to questions about what's expected of local companies and agencies in the wake of a data breach.
"There is no enacted law that compels a public or private entity to reveal details of a data breach," an unattributed response from the agency explained.
"The TT-CSIRT does not have the legal authority to initiate a criminal investigation (this is the responsibility of the TTPS Cyber and Social Media Unit), nor does it have the authority to initiate investigations under the Data Protection Act (that is the responsibility of the Office of the Information Commissioner – which has not been established)."
The TTCSIRT said that it contacted Massy after the April incident and were supplied with a copy of the media release. In July, TTCSIRT reviewed the proof pack. The agency then unofficially offered Massy advice based on their investigation of the October data dump.
"The TT-CSIRT does not have the legal authority to force any private entity to comply with its guidance. Any entity has a duty to its employees and the people they serve. It is the civil responsibility of the entity to assess the extent of the breach, determine and notify the affected parties and provide a mechanism which can assist affected persons to monitor their information for identity theft."
Mark Lyndersay is the editor of technewstt.com. An expanded version of this column can be found there.


Comments
"Stonewalling & silence over data breaches"