Hack mischief
Only four of the 11 government websites hacked by Brazilian hackers this week have been restored.
Up to yesterday only the TT Police Service, Tourism Ministry, Office of the Prime Minister, and National Energy websites were operational.
Both the Citizen Security Programme and the immigration sites displayed an “Error 404" message indicating that the link is dead or broken, while the Office of the Attorney General and the Telecommunications Authority sites indicated that the “site can’t be reached.” meanwhile the Nedco site was temporarily down for maintenance and the national security link automatically rerouted users to its Facebook page.
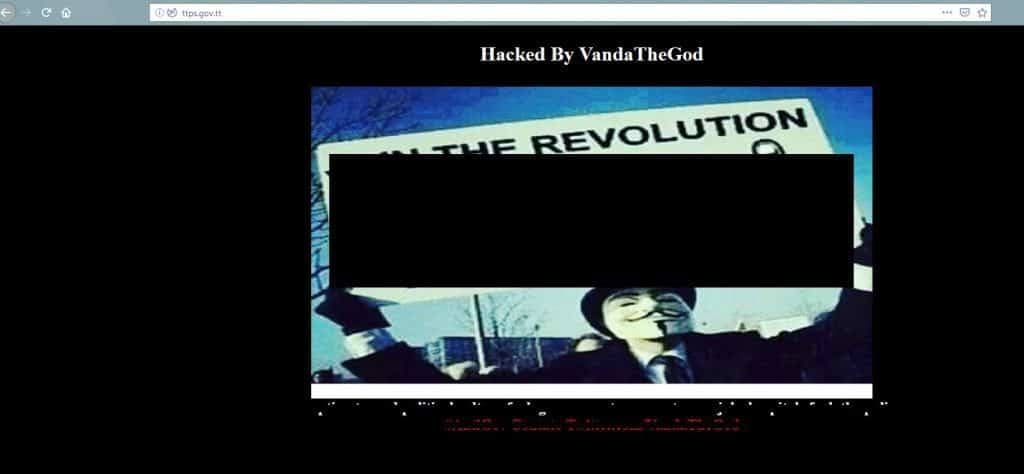
Brazilian hacker or hackers, VandatheGod, took responsibility for the hack on social media platform, Twitter. On a number of the websites VandatheGod posted an image of a man wearing a Guy Fawkes mask and holding the sign "Join the Revolution, Tell Your Corrupt Government to F--- Off".
In a previous article it was noted, “Attorney General Faris Al-Rawi also told Newsday the ministry’s official site, legalaffairs.gov.tt, was hacked but the IT department got to work and there was no reported damage to the site. He said he was awaiting a physical report on the incident.”
It also stated that at the post-Cabinet media conference on Thursday National Security Minister Stuart Young confirmed the national security ministry and immigration division websites had both been hacked, but said no real damage had been done.
Asked yesterday about measures against further cyber attacks Young told Sunday Newsday, “The Government is conscious of the attacks. At the Ministry of National Security I have received preliminary reports and I am awaiting further reports, including recommendations. This mischief is being taken seriously. I will refrain from any further comment at this stage.”
Anil Ramnanan, systems administrator at the University of the West Indies Open Campus explained that usually hackers looked for websites with vulnerabilities, which can happen when the website software has not been updated in a while. They could scan websites for those vulnerabilities and run software to compromise and deface the websites.
He said that was most likely what happened with the Government sites mentioned above.
In terms of security he said, “If proper best practice was used to set up these websites then they shouldn’t contain any kind of personal information like user names or passwords. If they had other internal information like login information stored on those servers, that could have been compromised. The thing is I don’t know if these websites had that kind of information but if they did, whoever was able to compromise the websites may have been able to access that.”
He said the best case scenario was that the websites had only general information for public consumption and that information got wiped out. He said mitigating such actions in the future was as simple as changing passwords, updating the software on the websites, and removing vulnerabilities.
Ramnanan said vulnerabilities that could have given hackers access included not setting up the login page correctly. He said if it was not, it could be manipulated by a hacker which would give them access to other areas of the site.
“They may not even have to hack it and it may not even necessarily be a problem with the software. It could be something as simple as someone using a bad password – someone set their password as 12345 or something like that – and they got in like that.”
Another option was that the website software could have been misconfigured so the software permissions were not set correctly and was accessible to others. He added that it seemed as if the “hacked” sites used similar software. If one person or company created them all, they could have used the same password for all the sites so that when the hacker found out one password they tried it elsewhere and was able to access all.


Comments
"Hack mischief"